4 Ways to Keep Hybrid Workers and Critical Systems Secure in 2022
IT departments and managers can take these basic steps to ensure hybrid workers are protected from cyber attacks and other security vulnerabilities.
By Vanessa Godsal
US hybrid workers are (hopefully) closing down their laptops for the winter holidays, but before they do, they should check in with their hardworking IT security teams to make sure everything is buttoned up before heading into the new year.
That’s because sophisticated cyber attacks have been ramping up over the past year, and aren’t likely to slow down in 2022, security experts are saying.
Just last week, senior White House cyber official Jen Easterly warned executives from major US industries that they need to take action to address “one of the most serious” vulnerabilities she has seen.
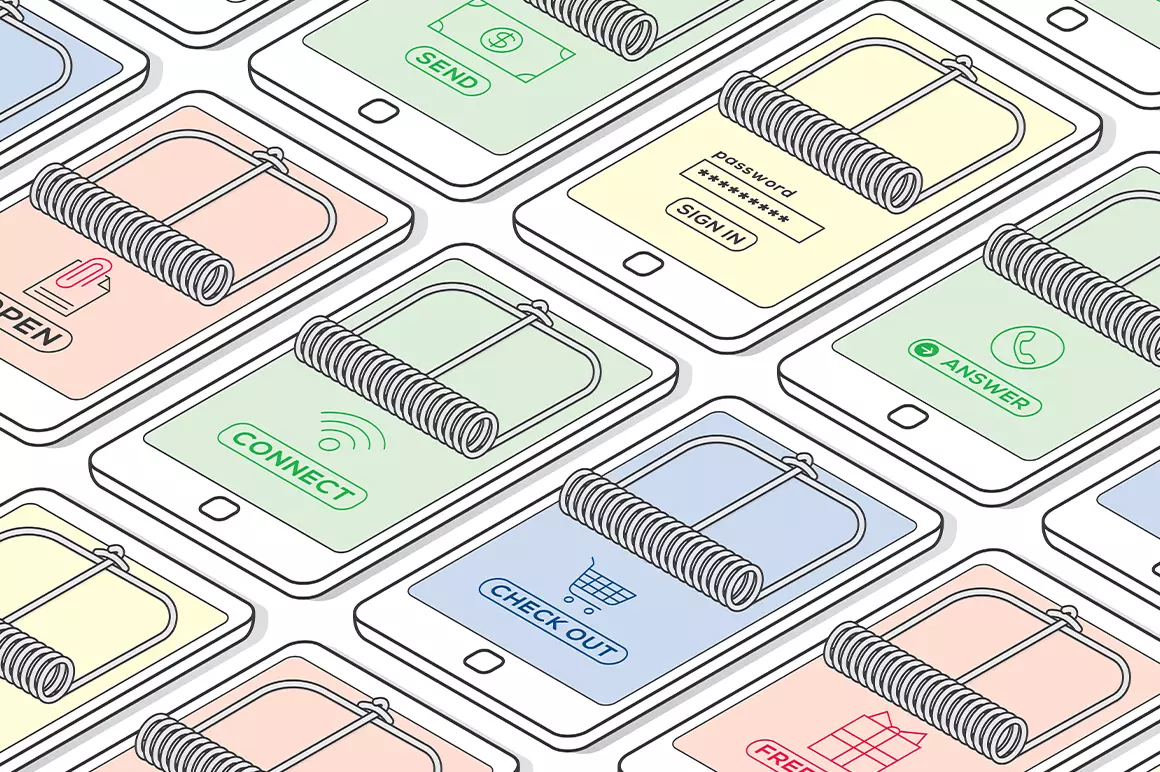
Especially at risk is what IT departments call “the corporate perimeter,” the end-user devices like laptops, printers, and corporate smartphones that are the most exposed.
From phishing scams around upcoming global events to the security of a permanent hybrid workforce, it will be more important than ever for organizations to protect data and ensure the continuation of critical infrastructure and workflows.
Here are the four most important things IT managers can do:
Defend hybrid workers
Some 61% of remote workers anticipate working in this way in 2022 and beyond. But doing so will perpetuate many of the associated risks that emerged over the past two years. And major events like the Winter Games and the FIFA World Cup will provide plenty of opportunities for new phishing lures. Home workers are often distracted, making them prone to engage in risky behavior like using unsecured personal devices for work.
Too many organizations erroneously think being behind a firewall is enough to keep an endpoint safe. In fact, they should be embedding zero trust principles into the endpoint, at a device firmware, OS and app layer. Access to individual services should be controlled on a case-by-case basis according to verification of user, device and security posture.
Protect your device firmware
Organizations often neglect firmware patching, with devices such as printers and scanners easily overlooked. That’s a major risk when compromise at this layer could be used to achieve long-term persistence and enable destructive attacks. There’s a real concern that sophisticated Tactics, Techniques and Procedures (TTPs) that target PC firmware could trickle down from nation states to become more widely adopted by organized criminals in ransomware attacks.
RELATED: Why home security is paramount—now more than ever
To address this, organizations need firmware protection based around visibility and control. That means the ability to self-heal firmware if it’s interfered with by malware, as well as in-memory breach detection, and automated alerting. It also means instant-on security which immediately configures devices to corporate policy as soon as they’re added to a network.
Guard your software supply chain
From Kaseya to Log4J and SolarWinds, we saw a new high-water mark in supply chain attacks. It’s not only software providers that are at risk. One report warned of growing attempts to implant malware in open-source code repositories, noting such attacks had surged 650% in just a year. Both SMBs and high-profile targets will be at risk in 2022, and organizations with multiple IT partners will be particularly exposed. Now that a blueprint has been created for monetizing such attacks, they will certainly become more widespread.
Enhancing the security of DevOps processes is one way to mitigate. But no single method can eliminate supply chain risk. CIOs must therefore focus on overhauling IT architecture to reduce the attack surface. That means fine-grained network segmentation, principles of least privilege, and mandatory access control.
Be alert to ransomware ‘pile-ons’
When an organization has been compromised by ransomware actors, others may look to repeat the trick in the succeeding weeks and months. These “pile-ons” could be accompanied by efforts to increase pressure on victims to pay — such as by cold calling partners and customers. A thriving black market in network access and other services will open the door to many more cybercrime groups.
Endpoints account for 70% of successful breaches, with malware usually arriving via email attachments, malicious links and downloadable files. While detection will always be a vital part of security, relying on detection-alone isn’t enough. Reducing the attack surface by applying threat containment to protect the most common attack vectors — i.e. email, browsers and downloads — is a must.
The endpoint is the axis where threats, users and technology meet. And that’s where defensive efforts should be focused in 2022 and beyond.

